Identity Crisis Part Two
by Michael Patrick O'Leary
This article appeared in Ceylon Today on Thursday October 6 2016
Someone is begging for money using my name. Some people really believe he is me. On several occasions, I have had to answer some testing questions from people I have known for a long time in real life. This is reasonable enough and I could easily convince them that I am the man they know.
It is not so easy to convince Facebook and on 27 September I was expelled from that community. Dealing with Facebook and Google one enters the world of Kafka.
Der Prozess
In The Trial by Franz Kafka, Joseph K is arrested by two warders “one fine morning,” although he has done nothing wrong. The German title, Der Prozess, connotes both a “trial” and a “process”: the machinery has been set in motion, and the process will grind toward conclusion. The examining magistrate tells K that he has seriously damaged his own case by his behaviour. Everyone who knows K also knows about his trial. From his point of view, the entire universe finds him guilty. He is taken to a quarry by two men who stab him to death. At least my unfair trial by Facebook only led to this: “We’ll get in touch with you at the email address you provided after we’ve reviewed your ID. You will now be logged out of Facebook.”
I am grateful that, on this “fine morning”, I am not a corpse in a quarry, merely a live one in a quandary.
Positive and Negative
The experience of having a faceless stranger’s grubby fingers rifling through one’s life is very distasteful. There have been some positive aspects, however. I have reestablished contact with a lot of real-life friends from whom I had not heard for a long time. Thank you for that Mr PH (Personal Hacker). Soon after I was alerted that I had been hacked, I started receiving many supportive phone calls – from Ireland, Thailand, Sri Lanka, the US and the UK. Two different bank managers called me. One real-life friend in Sri Lanka telephoned and was surprised when I answered the phone. She really though I was stranded in Cyprus and had been making arrangements for her daughter in the UK to send ‘me’ a payment. I was touched by this but puzzled that an astute professional could be so gullible. When I met her last week she showed me the e-mails the hacker had sent.
I understood why she had believed the hacker. One e-mail said “Dear B, Can I call you on this line (he quoted her office phone number) X (that’s my wife) extends her sincere greetings and gratitude for all your concern and assistance”. Another e-mail to B gave details of our attempt to purchase a property and to dispose of our current home. There were enough errors in his e-mails to indicate that the writer was not me. Nevertheless, it is creepy to be aware that he is obviously ploughing through my personal correspondence and putting together a faux persona that convinces some.
Customer Service
My real-life and virtual friends responded sympathetically to my plight but many were far too optimistic about how easy it is to deal with such a situation. People told me that the first thing to do was to report the breach to Facebook and Google because those organisations have solid systems in place to handle account hacking. I would certainly expect them to have solid systems in place but I was not able to utilise them.
If my credit card were stolen I would be expected to notify the provider immediately. I have found it impossible to notify Google or Facebook that my identity has been stolen. I have attempted the cumbersome recovery procedure several times. I am told it has been successful but then I have to enter a verification code sent to my mobile phone. I cannot do this because my friendly neighbourhood PH has replaced my mobile phone number with his.
Horse Bolted. Lock the Stable Door
The Google and Facebook help pages confine themselves to giving useless advice about preventing future hacks rather than dealing with the specific hack that has already happened. I had anyway followed the advice. I never share my passwords with anyone, even my wife. I had recently changed my passwords several times. There is nothing personal in the passwords. They are rated as ‘strong’ because they are totally random and contain mixtures of letters, digits and symbols. I could not hope to remember them myself, so I do not understand how anyone else could guess them.
Who Cares about Customers?
This kind of scam has been going on for many years. I have received many such messages myself. The modus operandi is to send an e-mail to my contacts asking why the hacker posing as me has not received a reply to a previous (non-existent) e-mail. He has got my friends’ addresses from my G-Mail accounts which he has hacked. However, he does not use my G-mail addresses to write to my contacts. He has set up new accounts with addresses that differ from my addresses by just one character. The recipient generally does not realise the discrepancy and even if they do they dismiss it as an error.
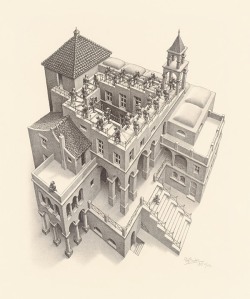
One friend wrote to me: “Surely G-Mail have some idea who he is and where he is from these newly created accounts?” I would have thought so but experts advise me that Google would not seek such information without a court order. The perpetrator’s human rights get more protection than the victim’s. It is impossible for me to report this to G-Mail. I just get sent around in a loop and fail at the end. I am reminded of those so-called “impossible constructions” by MC Escher, such as Ascending and Descending and Relativity. There appears to be a lot of information on the G-Mail and Facebook help pages but there is no e-mail address or telephone number. There is at Google or Facebook no human being with whom to discuss the identity theft. This kind of scam has been the subject of numerous articles over the years and the boffins at Google and Facebook must be clever enough to stop it. They haven’t stopped it because they don’t care. It is not harming profits.
You Are Who?
While many pooh-poohed the idea, I wondered from the outset whether this hacker had some personal grudge against me. Like the pooh-poohers, I had seen many examples of this kind of scam before. Nevertheless, I was surprised at his persistence. The messages have been going out for three months and, at the time of writing, show no signs of stopping.
A real-life friend tried to engage with my PH and got a threatening response. All pretence of being me was dropped: Using the name “Spitfire” he sent this message: “Maybe you should just mind your business because your email might be next.PS: tell your friend that this is what happens when he tries to recover the email i already hacked into. If he tries recovering it with any other email then he looses that one too!”
In the first debate with Hillary Clinton, Donald Trump visualised a stereotypical hacker: “It could be someone sitting on their bed that weighs four hundred pounds.” One of the hackers who recently intruded on President Sirisena’s official website was a seventeen-year-old boy. Mat Honan is digital savvy enough to write regularly for Wired magazine- but he still got hacked: “In the space of one hour, my entire digital life was destroyed”. Honan managed to establish some contact with his hacker whom he calls Phobia. Phobia was 19 years old.
A real-life friend speculated about the identity of my PH: “This smacks of an IT support type person who has had an opportunity to either get third party access to your hardware or even direct access during a mend or upgrade.” I followed up on this line of thinking. My desktop PC was indeed in a shop being repaired when the hacking occurred. It would have been easy for one of the technicians to log into my G-Mail accounts because the system remembered the passwords. Once in, he could change my passwords because he knew my mobile phone number. He could then use two-step authentication to override my mobile phone number.
I went to the shop and explained to one of the managers and a technician what had happened. They said it could not have happened there. Three brothers have been running the business for 15 years (they have always been helpful to me and are often reluctant to charge for their service) and they said they had never experienced anything like this before. Their technicians have been with them a long time and are completely trustworthy – they would say that wouldn’t they? The technician showed no sign of guilt and told us about a CID unit that investigated this kind of hacking. We had expected the messages to stop after letting the shop know that we knew. In fact, incidents gathered pace.
Next week I explore the psychopathology of the hacker. Why on earth do they do it? What kind of moral universe do they inhabit?




I’ve tried t find You, but failed. Can You please send me a friend request.
LikeLike
As I have said before Mark, I cannot access Facebook at all. You can contact me by e-mail at bartleby@post.com
LikeLike
I recall writing to you – or trying to write to you! – when I first received a message from your PH. The message was well enough written to make me do a double-take (could Michael REALLY be stuck in Cyprus and asking for a loan?) but then the sheer implausibility of the situation moved me to alert you to what was happening. But I don’t suppose you got the message since PH had damaged your communications.
LikeLike
You are right Mark. I still cannot access my G-Mail accounts and have been expelled from Facebook because of the hacker.He was plausible enough for our lawyer to make arrangements to send him money.He was obviously reading through the communications I had with her and picked up enough personal information about me and my wife to fool someone who knows us well in real life.
LikeLike